GATE Mechanical Engineering Conceptual Questions: A Comprehensive Plan
Preparing for GATE ME requires focused practice with conceptual questions. Accessing previous years’ papers in PDF format, from 1987-2024, is crucial for understanding exam patterns and difficulty levels.
ExamSIDE.com and Ace Publications offer chapter-wise organized resources. These materials, including solved questions from 2010-2018, enhance preparation and boost your overall score.
GATE (Graduate Aptitude Test in Engineering) Mechanical Engineering (ME) demands a strong grasp of fundamental concepts, moving beyond rote memorization. Success hinges on the ability to apply theoretical knowledge to solve complex, real-world engineering problems. This necessitates a dedicated focus on conceptual understanding, and utilizing resources like previous year question papers in PDF format is paramount.
The examination increasingly emphasizes application-based questions, requiring candidates to demonstrate a deep understanding of core mechanical engineering principles. Simply memorizing formulas is insufficient; you must be able to reason through problems and justify your solutions.
Accessing a comprehensive collection of past GATE ME papers (1987-2024), readily available as downloadable PDFs from platforms like ExamSIDE.com and Ace Publications, provides invaluable insight into the exam’s evolving pattern. These resources showcase the types of conceptual questions frequently asked, allowing you to tailor your preparation accordingly.
Furthermore, analyzing solved papers from 2010-2018, as offered in chapter-wise formats, helps identify key topics and common question styles. This focused approach, combined with consistent practice, is essential for achieving a high score in the GATE ME examination.
II. Importance of Previous Year Question Papers
Previous year GATE ME question papers are indispensable for effective preparation. They serve as the most authentic source for understanding the exam’s structure, difficulty level, and frequently tested concepts. Accessing these papers, often available as downloadable PDFs, allows candidates to familiarize themselves with the question types and marking scheme.
Analyzing papers from 1987 to 2024, as curated by resources like Ace Publications, reveals evolving trends in the exam. This historical perspective is crucial for identifying consistently important topics and anticipating future question patterns. Furthermore, solving these papers builds confidence and improves time management skills.
ExamSIDE.com provides chapter-wise organized past papers, facilitating targeted practice. Utilizing solved papers (e.g., those from 2010-2018) allows for self-assessment and identification of knowledge gaps.
The GATE 2026 ME exam, as indicated by recent information, is expected to be of moderate to tough difficulty, with a strong emphasis on conceptual clarity. Therefore, consistent practice with previous papers is not merely recommended, but essential for success.
III. Understanding the Exam Pattern & Difficulty Level (2026 Perspective)
The GATE Mechanical Engineering exam maintains a consistent pattern: 65 questions carrying 100 marks, with a duration of three hours. The paper is divided into General Aptitude (15 marks) and core Mechanical Engineering subjects (85 marks). However, the difficulty level is subject to change, requiring adaptive preparation.
Recent analyses suggest the 2026 exam will likely be moderate to tough, with a significant emphasis on conceptual understanding rather than rote memorization. This necessitates a deep grasp of fundamental principles and the ability to apply them to solve complex problems. Access to previous year question papers in PDF format is vital for gauging this expected difficulty.
Resources like ExamSIDE.com and Ace Publications offer comprehensive collections of past papers (1987-2024) which help in understanding the evolving exam trends.
Focusing on solved papers, particularly those from recent years, will provide insights into the types of conceptual questions frequently asked. Mastering these concepts, alongside consistent practice, is key to achieving a good score in GATE 2026.
IV. Core Mechanical Engineering Subjects & Conceptual Focus
GATE Mechanical Engineering covers a broad spectrum of subjects, demanding a strong conceptual foundation in each. Key areas include Engineering Mechanics, Strength of Materials, Theory of Machines, Thermodynamics & Heat Transfer, Fluid Mechanics, Manufacturing & Production Engineering, and Machine Design;
Conceptual focus is paramount. Expect questions testing your understanding of underlying principles rather than direct formula application. For example, in Thermodynamics, understanding cycles and laws is more crucial than memorizing specific values. Similarly, in Fluid Mechanics, flow analysis and boundary layer concepts are vital.
Utilizing previous year question papers (available in PDF format) reveals the relative importance of each subject. Resources like ExamSIDE.com provide chapter-wise breakdowns, aiding focused preparation. Ace Publications’ collection (1987-2024) offers a historical perspective on question trends.
Mastering these core subjects requires a thorough understanding of fundamental concepts, coupled with consistent practice using solved examples and past GATE papers. This approach ensures you’re well-equipped to tackle the conceptual challenges of the exam.
A. Engineering Mechanics
Engineering Mechanics forms the bedrock of Mechanical Engineering, demanding a firm grasp of statics and dynamics. GATE often tests conceptual understanding of forces, moments, friction, and their applications to real-world scenarios. Expect questions involving free body diagrams, equilibrium conditions, and kinematic/kinetic analyses.
Conceptual problems frequently involve determining reactions in beams and frames, analyzing the motion of particles and rigid bodies, and understanding concepts like work-energy principle and impulse-momentum. The ability to apply these principles to complex systems is crucial.
Previous year GATE question papers (available in PDF format) consistently feature problems from this area. Analyzing these papers reveals a focus on understanding fundamental concepts rather than rote memorization of formulas. Resources like ExamSIDE.com offer chapter-wise categorized questions.
Effective preparation involves practicing a wide range of problems, focusing on building a strong intuitive understanding of the underlying principles. Mastering this subject is essential for success in subsequent mechanical engineering courses and the GATE exam itself.
B. Strength of Materials
Strength of Materials (SoM) is a vital component of the GATE ME syllabus, focusing on the behavior of solid materials under stress and strain. Conceptual understanding is paramount, as the exam frequently tests the application of principles rather than direct formula application.
Key areas include stress, strain, elastic constants, bending moments, shear forces, torsion, and failure theories. Expect questions involving the analysis of beams, shafts, and other structural elements under various loading conditions. Understanding concepts like stress concentration and deflection is also crucial.
GATE question papers (available as PDFs) consistently demonstrate a preference for problems requiring a deep understanding of these concepts. Resources like Ace Publications provide meticulously arranged, subject-wise questions.
Effective preparation necessitates practicing problems that require applying fundamental principles to determine stresses, strains, and deflections in various mechanical components. A strong foundation in SoM is essential for tackling more advanced topics like Machine Design.
C. Theory of Machines
Theory of Machines (ToM) demands a strong grasp of kinematic and dynamic principles governing the motion of mechanical systems. GATE ME frequently assesses the ability to analyze mechanisms, linkages, cams, gears, and governors.
Conceptual understanding is key, focusing on velocity and acceleration analysis, force analysis, and the application of concepts like Coriolis acceleration. Expect questions involving the determination of degrees of freedom, transmission ratios, and the design of mechanisms for specific motion requirements.
Previous year GATE question papers (in PDF format) consistently feature problems requiring a thorough understanding of these concepts. Resources like ExamSIDE.com offer chapter-wise organized questions, aiding focused preparation.
Effective preparation involves practicing problems that require applying kinematic equations, analyzing gear trains, and understanding the dynamic behavior of mechanisms. A solid foundation in ToM is crucial for success in Machine Design and related areas.
D. Thermodynamics & Heat Transfer
Thermodynamics and Heat Transfer form a significant portion of the GATE ME syllabus, demanding a firm understanding of fundamental principles and their applications. Expect conceptual questions revolving around thermodynamic cycles (Carnot, Rankine, Brayton), laws of thermodynamics, and various heat transfer modes (conduction, convection, radiation).
Conceptual clarity is vital when tackling problems related to entropy, enthalpy, and the analysis of thermodynamic processes. Heat transfer questions often involve calculating heat transfer rates, understanding thermal resistance, and applying concepts like boundary layers.
Utilizing previous year GATE question papers (available in PDF format) is crucial for familiarizing yourself with the exam pattern and difficulty level. Resources like Ace Publications provide a comprehensive collection of these papers, organized subject and chapter-wise.
Effective preparation requires practicing problems involving cycle analysis, heat exchanger design, and the application of Fourier’s law, Newton’s law of cooling, and Stefan-Boltzmann law.
E. Fluid Mechanics
Fluid Mechanics is a core subject in GATE ME, frequently testing candidates on their grasp of fundamental concepts like fluid properties, fluid statics, and fluid dynamics. Expect conceptual questions focusing on flow analysis, boundary layers, and various fluid flow phenomena.
A strong understanding of Bernoulli’s equation, Navier-Stokes equations, and dimensional analysis is essential. Questions often involve calculating pressure drop, flow rate, and forces exerted by fluids. The concept of viscosity and its impact on fluid behavior is also frequently tested.
Leveraging previous year GATE question papers (available as PDFs) is paramount for understanding the exam’s emphasis on conceptual application. Resources like ExamSIDE.com offer well-organized, subject-wise collections of these papers.
Effective preparation involves solving problems related to pipe flow, open channel flow, and the analysis of fluid machinery like pumps and turbines. Mastering concepts like turbulence and laminar flow is also crucial for success.
F. Manufacturing & Production Engineering
Manufacturing & Production Engineering consistently features in GATE ME, demanding a solid understanding of various manufacturing processes, machine tools, and automation techniques. Conceptual questions often revolve around process selection, optimization, and quality control.
Key areas include machining, casting, forming, joining, and additive manufacturing. Expect questions assessing your knowledge of process parameters, tooling, and material behavior during manufacturing; Understanding concepts like Taylor’s tool life equation and surface roughness is vital.
Utilizing previous year GATE question papers (available in PDF format) is crucial for identifying frequently tested topics. Resources like ExamSIDE.com provide organized collections of these papers, categorized by subject and chapter.
Effective preparation involves mastering concepts related to production planning, inventory control, and statistical quality control. Familiarity with automation technologies like CNC machines and robotics is also essential for tackling complex problems.
G. Machine Design
Machine Design is a significant component of the GATE ME syllabus, frequently testing candidates on their ability to analyze stresses, select appropriate materials, and design machine elements. Conceptual understanding is paramount, moving beyond mere formula application.
Core topics include the design of shafts, gears, bearings, clutches, and brakes. Expect questions focusing on failure theories, fatigue analysis, and the application of design factors. Understanding concepts like stress concentration and torsional shear stress is crucial.
Leveraging previous year GATE question papers (available as PDFs) is essential for familiarizing yourself with the exam pattern and difficulty level. Resources like Ace Publications offer comprehensively curated collections spanning 1987-2024.
Effective preparation requires a strong grasp of material properties, manufacturing processes, and design standards. Practice solving problems involving component design, analysis, and optimization to enhance your problem-solving skills and conceptual clarity.
V. Detailed Subject-Wise Conceptual Areas
Mastering GATE ME demands a deep dive into subject-specific conceptual areas. Utilizing previous year question papers in PDF format is vital for identifying frequently tested concepts and understanding the exam’s emphasis.
Focus on fundamental principles rather than rote memorization. For example, in Thermodynamics, understand cycles and laws beyond just equations. In Fluid Mechanics, grasp flow analysis and boundary layers conceptually.
Resources like ExamSIDE.com provide chapter-wise organized questions with solutions, aiding focused preparation. Ace Publications offers a comprehensive collection from 1987-2024, enabling thorough practice.
Conceptual clarity in Engineering Mechanics (statics & dynamics), Strength of Materials (stress, strain, failure theories), and Theory of Machines (kinematics & dynamics) is crucial. Similarly, Manufacturing processes and Machine Design require a strong foundational understanding.
Prioritize understanding the ‘why’ behind the formulas, not just the ‘how’. This approach will enable you to tackle complex, conceptual problems effectively in the GATE exam.
A. Engineering Mechanics: Statics & Dynamics Concepts
Engineering Mechanics forms a foundational pillar for GATE ME, demanding a strong grasp of statics and dynamics concepts. Previous year question papers, readily available in PDF format, reveal a consistent focus on these areas.
Statics requires understanding equilibrium conditions, free body diagrams, and the resolution of forces. Conceptual questions often involve analyzing truss structures, beams, and friction problems.
Dynamics necessitates a firm understanding of kinematics and kinetics, including motion analysis, work-energy principles, and impulse-momentum methods. Expect questions involving particle and rigid body dynamics.
Resources like ExamSIDE.com offer chapter-wise questions with detailed solutions, aiding targeted practice. Ace Publications’ compilation (1987-2024) provides a vast pool of problems for comprehensive preparation.

Focus on applying fundamental principles to solve real-world engineering problems. Conceptual understanding is key to tackling complex scenarios beyond simple formula application. Mastering these concepts is vital for success.
B. Strength of Materials: Stress, Strain & Failure Theories
Strength of Materials is a crucial component of the GATE ME syllabus, heavily emphasizing stress, strain, and failure theories. Access to previous year question papers in PDF format is invaluable for focused preparation.
Conceptual understanding of normal and shear stresses, strain energy, and bending moments is essential. Questions frequently assess the ability to analyze stresses in composite structures and thin-walled pressure vessels.
Failure theories, including maximum shear stress theory, distortion energy theory, and Rankine’s theory, are consistently tested. Expect problems requiring the application of these theories to predict material failure under complex loading conditions.

Resources like ExamSIDE.com provide chapter-wise solved questions, enabling targeted practice in specific areas. The comprehensive collection from Ace Publications (1987-2024) offers a wide range of problems.
Focus on developing a strong intuitive understanding of material behavior under load. This will allow you to effectively solve conceptual problems and avoid rote memorization of formulas.
C. Theory of Machines: Kinematics & Dynamics of Mechanisms
Theory of Machines demands a firm grasp of kinematics and dynamics of mechanisms, frequently tested in GATE ME. Utilizing previous year question papers in PDF format is paramount for effective preparation and understanding the exam’s focus.
Kinematics problems often involve velocity and acceleration analysis of linkages, cams, and gears. Expect questions requiring the application of relative velocity and acceleration methods.
Dynamics focuses on forces and moments in mechanisms, including balancing of rotating and reciprocating masses. Understanding concepts like dynamic force analysis and governors is crucial.
Resources such as ExamSIDE.com offer chapter-wise solved papers, allowing targeted practice in specific areas like gears and cam mechanisms. Ace Publications’ collection (1987-2024) provides a broad spectrum of problems.
Conceptual clarity regarding degrees of freedom, Gruebler’s equation, and transmission ratios is vital. Practice solving problems involving complex mechanisms to build confidence and analytical skills.
D. Thermodynamics: Cycles, Laws & Applications
Thermodynamics is a cornerstone of Mechanical Engineering, heavily featured in GATE ME. Mastering thermodynamic cycles, laws, and their practical applications is essential for success. Accessing previous year question papers in PDF format is vital for focused preparation.
Expect questions on various cycles – Carnot, Rankine, Otto, Diesel, and Brayton – requiring calculations of efficiency and work output. A strong understanding of the underlying principles is crucial.
The laws of thermodynamics (Zeroth, First, Second, and Third) are frequently tested, often in conceptual problem-solving scenarios. Entropy and its implications are also important.
Resources like ExamSIDE.com provide chapter-wise solved papers, enabling targeted practice on specific topics like psychrometry and combustion. Ace Publications’ comprehensive collection (1987-2024) offers diverse problem sets.
Conceptual clarity on concepts like irreversibility, availability, and heat engines is paramount. Practice applying these principles to real-world engineering systems to enhance problem-solving abilities.
E. Fluid Mechanics: Flow Analysis & Boundary Layers
Fluid Mechanics is a significant component of the GATE ME syllabus, demanding a firm grasp of flow analysis and boundary layer theory. Utilizing previous year question papers in PDF format is crucial for effective preparation.
Expect questions on fluid statics, kinematics, and dynamics, including concepts like pressure distribution, buoyancy, and fluid acceleration. Understanding Bernoulli’s equation and its applications is vital.
Boundary layer theory is frequently tested, focusing on concepts like boundary layer thickness, skin friction, and separation. Questions often involve calculations of drag and lift forces.
Resources like ExamSIDE.com offer chapter-wise solved papers, allowing targeted practice on topics like pipe flow, open channel flow, and dimensional analysis. Ace Publications’ extensive collection (1987-2024) provides diverse problem sets.

Conceptual understanding of concepts like viscosity, turbulence, and flow regimes is paramount. Practice applying these principles to real-world fluid flow scenarios to improve problem-solving skills.
F. Manufacturing: Processes, Machines & Automation
Manufacturing Engineering forms a core part of the GATE ME exam, requiring a strong understanding of various processes, machines, and automation techniques. Access to previous year question papers in PDF format is essential for targeted preparation.
Expect questions covering traditional manufacturing processes like casting, forming, machining, and joining. Understanding the principles behind each process, along with their advantages and limitations, is crucial.
Modern manufacturing techniques, including CNC machines, robotics, and automation systems, are also frequently tested. Questions may involve calculations related to machining time, material removal rate, and automation efficiency.
Resources like ExamSIDE.com provide chapter-wise solved papers, enabling focused practice on specific manufacturing topics. Ace Publications’ comprehensive collection (1987-2024) offers a wide range of problems.
Conceptual clarity on topics like metrology, quality control, and production planning is vital. Practice applying these concepts to optimize manufacturing processes and improve product quality.
G. Machine Design: Component Design & Analysis
Machine Design is a significant component of the GATE ME syllabus, demanding a firm grasp of component design principles and analytical methods. Utilizing previous year question papers in PDF format is paramount for effective preparation.
Expect questions focusing on stress analysis, failure theories, and the design of machine elements like shafts, gears, bearings, and springs. Understanding material properties and their influence on design is crucial.
Finite element analysis (FEA) concepts and their application to component design are increasingly important. Questions may involve interpreting FEA results and optimizing designs based on stress concentrations.
Resources such as ExamSIDE.com offer chapter-wise solved papers, allowing focused practice on specific machine design topics. Ace Publications’ extensive collection (1987-2024) provides a diverse problem set.
Conceptual understanding of topics like fatigue, vibration, and dynamic loading is vital. Practice applying these concepts to ensure the reliability and durability of machine components.
VI. Analyzing GATE Questions (1987-2024)
A thorough analysis of GATE Mechanical Engineering questions from 1987 to 2024 is fundamental to understanding the exam’s evolving trends and difficulty levels. Accessing these past papers, often available in PDF format, is the first step.
Focus on identifying recurring themes and frequently tested concepts. Note the shift in emphasis over the years – are there newer topics gaining prominence? Are certain areas consistently weighted more heavily?
Pay attention to the question types: multiple-choice, numerical answer, and linked answer questions. Understand the marking scheme and strategize accordingly.
Resources like Ace Publications provide a comprehensively curated collection of these past papers, organized subject and chapter-wise, facilitating focused analysis.
ExamSIDE.com also offers chapter-wise solutions, enabling you to pinpoint your weaknesses and refine your problem-solving skills. Identifying common mistakes made in previous attempts can prevent repeating them.
This historical analysis provides invaluable insights for targeted preparation and maximizing your GATE score.
VII. Topic-Wise Weightage Analysis (Based on Past Papers)
Determining the topic-wise weightage in GATE Mechanical Engineering is crucial for efficient preparation. Analyzing past papers (1987-2024), often found as PDFs, reveals consistent patterns in question distribution.
Core subjects like Engineering Mechanics, Strength of Materials, and Thermodynamics consistently hold significant weightage, demanding thorough conceptual understanding. Theory of Machines and Fluid Mechanics also appear frequently.
Manufacturing and Production Engineering, along with Machine Design, represent substantial portions of the exam, requiring detailed study of processes and design principles.
Resources like ExamSIDE.com offer chapter-wise breakdowns, aiding in identifying high-yield topics. Ace Publications’ curated collections also facilitate this analysis.
General Aptitude, while not directly mechanical, contributes a fixed percentage to the final score, necessitating dedicated practice. Prioritize topics with higher weightage while ensuring a balanced coverage of the syllabus.
This data-driven approach optimizes study time and maximizes your chances of success.
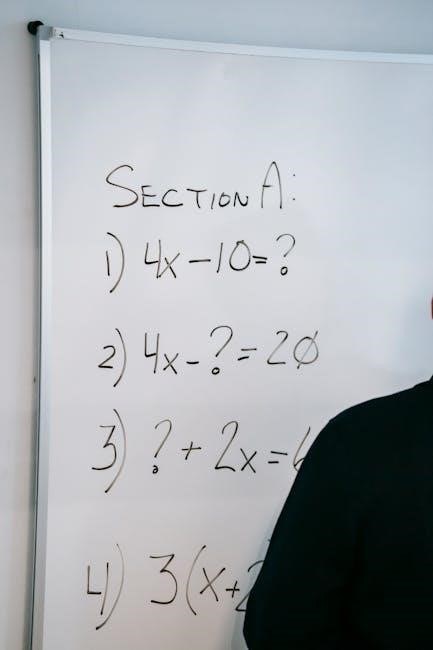
VIII. Common Conceptual Question Types in GATE ME
GATE Mechanical Engineering frequently tests conceptual understanding rather than rote memorization. Expect questions demanding application of fundamental principles to novel scenarios.
Engineering Mechanics often features problems on statics and dynamics, requiring free-body diagrams and kinematic analysis. Strength of Materials focuses on stress, strain, and failure theories, often presented in complex geometries.
Theory of Machines emphasizes kinematics and dynamics of mechanisms, testing understanding of velocity and acceleration analysis. Thermodynamics presents cycle analysis and application of laws, demanding problem-solving skills.
Fluid Mechanics questions assess flow analysis and boundary layer concepts, often involving complex fluid behavior. Manufacturing focuses on processes, machines, and automation, requiring knowledge of production techniques.
Machine Design tests component design and analysis, demanding application of design principles and material selection. Accessing past papers in PDF format (1987-2024) from resources like ExamSIDE.com and Ace Publications reveals these recurring question types.
Mastering these concepts is key to success.
IX. Strategies for Solving Conceptual Problems
Successfully tackling GATE ME conceptual problems demands a strategic approach. Begin by thoroughly understanding the fundamental principles underlying each topic – don’t just memorize formulas!
Visualize the problem: draw diagrams, free-body diagrams, or schematics to clarify the scenario. Break down complex problems into smaller, manageable steps. Identify the core concepts being tested and apply them systematically.
Practice with previous year question papers (1987-2024) in PDF format – resources like ExamSIDE.com and Ace Publications are invaluable. Focus on understanding the solution process, not just the final answer;
Analyze your mistakes: identify areas of weakness and revisit the underlying concepts. Time management is crucial; practice solving problems under timed conditions. Don’t be afraid to make assumptions, but clearly state them.
Regularly review solved papers to reinforce your understanding and identify common problem-solving techniques. Conceptual clarity is paramount; strive for deep understanding, not superficial knowledge.
Consistent practice builds confidence.
X. Utilizing Solved Papers for Effective Preparation

Leveraging solved GATE ME papers (available in PDF format from 1987-2024) is a cornerstone of effective preparation. These resources, readily accessible through platforms like ExamSIDE.com and Ace Publications, offer invaluable insights into the exam’s style and difficulty.
Don’t simply read the solutions; actively work through them. Attempt to solve the problem independently before reviewing the provided solution. This reinforces your understanding and identifies areas where you struggle.
Analyze the solution methodology: note the steps taken, the concepts applied, and the reasoning behind each decision. Pay attention to alternative approaches and their relative merits.
Categorize problems by topic and difficulty level to create a personalized study plan. Identify recurring themes and question types to focus your efforts. Use solved papers to assess your progress and track your improvement over time.
Regularly revisit previously solved papers to reinforce your knowledge and prevent forgetting. Treat solved papers as a learning tool, not just a source of answers.
Consistent review is key to success.
XI. Resources for GATE ME Question Papers & Solutions
A wealth of resources exists for accessing GATE Mechanical Engineering question papers and solutions, often available in convenient PDF format. Platforms like ExamSIDE.com provide chapter-wise organized previous year questions, complete with detailed solutions, spanning multiple years.
Ace Publications offers a comprehensive collection of GATE papers from 1987 to 2024, meticulously arranged by subject and chapter. These resources are invaluable for targeted practice and conceptual understanding.
Additionally, explore online forums and educational websites dedicated to GATE preparation. Many offer free access to sample papers and solved problems; Search for topic-specific PDFs covering areas like Thermodynamics, Fluid Mechanics, and Theory of Machines.
Remember to verify the authenticity and accuracy of the resources you utilize. Prioritize official GATE websites and reputable publishers. Utilize resources from 2010-2018 for focused practice.
Effective resource utilization is crucial for maximizing your preparation and achieving success in the GATE ME exam.
Strategic resource selection is key.
XII. The Role of General Aptitude in GATE ME
While GATE Mechanical Engineering heavily emphasizes technical proficiency, General Aptitude constitutes a significant 15% of the total marks. Neglecting this section can substantially impact your overall score and ranking. Therefore, dedicated preparation is essential;
General Aptitude assesses verbal and numerical reasoning skills, including data interpretation, analytical reasoning, and spatial visualization. These skills are crucial for effectively tackling complex engineering problems.
Although the focus is on technical subjects, a strong aptitude foundation enhances problem-solving abilities and improves time management during the exam. Resources offering practice questions and solved papers in General Aptitude are readily available online.
Integrating aptitude practice alongside your core mechanical engineering studies is a strategic approach. Allocate specific time slots for aptitude preparation and consistently evaluate your progress. Remember that conceptual clarity in both areas is vital.
Don’t underestimate the importance of aptitude; it can be the deciding factor in securing a favorable outcome in GATE ME.
A balanced approach is key to success.